Most vulnerability programs aren’t failing because teams don’t scan. They’re failing because teams can’t decide.
You end up with 10,000 findings, 200 “critical” CVEs, and exactly zero clarity for the board. Meanwhile, real risk creeps up quietly through exposed assets, weak compensating controls, and business-critical systems that don’t show up at the top of a CVSS-sorted list.
If you’re in fintech, banking, or healthcare: especially in regulated environments like the UAE: vulnerability prioritization is not an IT hygiene task anymore. It’s a capital allocation problem.
This post breaks down the 7 most common mistakes and gives you a board-ready fix: move from technical severity to financial narratives, using an AI-driven approach that ties vulnerabilities to business impact, compliance obligations, and ROI.
The board doesn’t buy CVSS. They buy decisions.
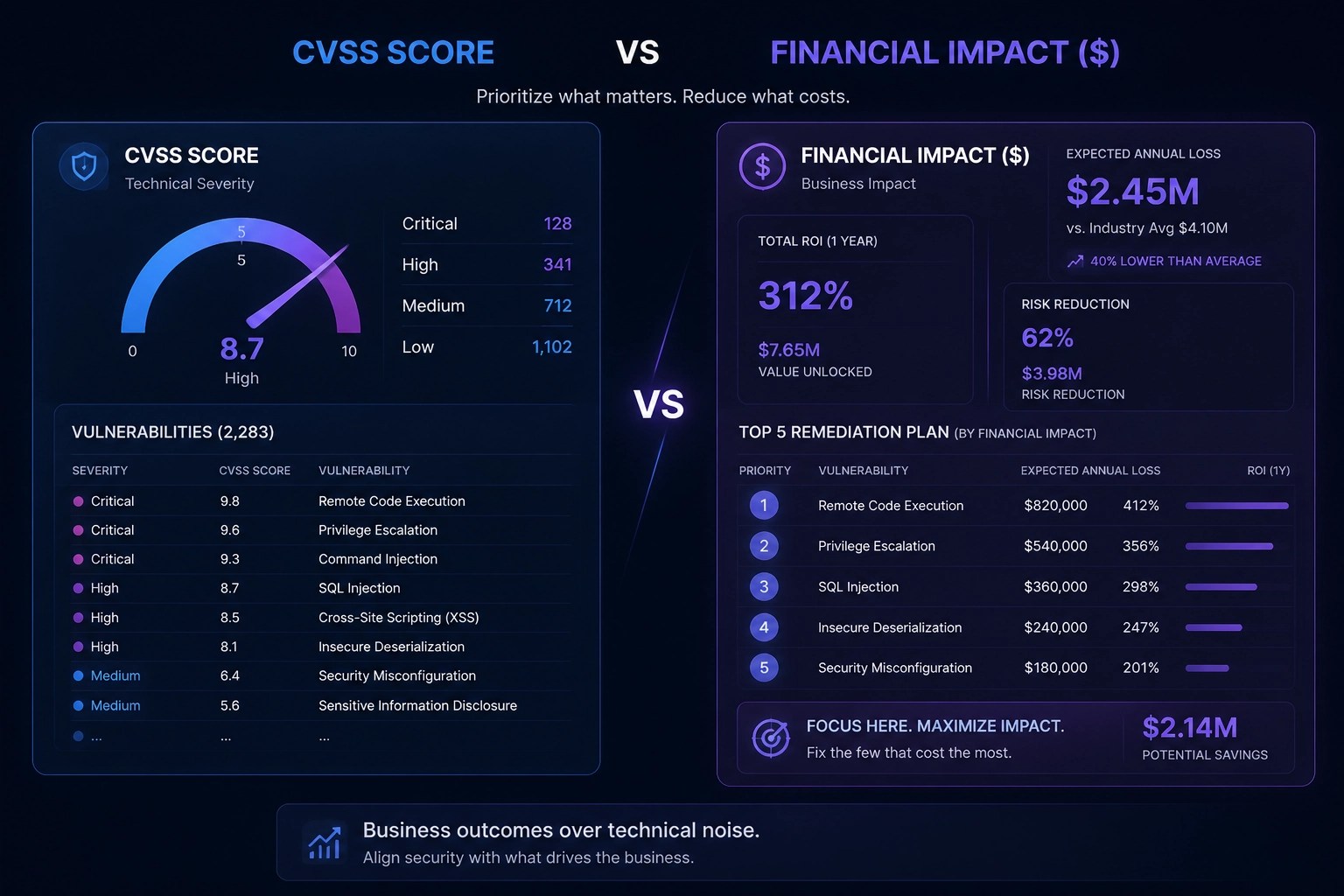
CVSS is a useful input. But it’s not a decision system.
The board wants answers like:
- “What’s our Expected Annual Loss if this weakness is exploited?”
- “What’s the cost to remediate vs. the risk reduction?”
- “What can we reduce in the next 30 days to materially lower exposure?”
- “Are we drifting out of compliance, and what’s the business impact?”
That’s where a modern vulnerability prioritization tool backed by AI, integrated into a GRC platform, and supported by cyber risk quantification software becomes the difference between a patching backlog and a real risk program.
(If you want to see what that looks like in practice, start here: https://www.observeri.com/.)
Mistake #1: You prioritize by CVSS score alone
What’s happening
Your queue is basically:
- Sort by CVSS (descending)
- Patch the “critical” ones
- Repeat next week
Why it fails
CVSS measures technical severity, not business risk. It doesn’t know:
- if the asset is internet-facing
- if exploit code exists
- if the system holds regulated data (PCI, HIPAA, GDPR)
- if compensating controls reduce likelihood
- if the service is mission-critical
A CVSS 9.8 on an isolated internal system can be less urgent than a CVSS 7.5 on a public-facing portal that touches payments or patient records.
How to fix it (board-ready)
Add context + economics:
- Asset criticality (revenue impact / operational dependency)
- Exposure (internet-facing, lateral movement paths)
- Threat intelligence (active exploitation, exploit availability)
- Control strength (MFA, segmentation, EDR coverage)
- Financial impact (loss magnitude and frequency)
This is the point where cyber risk quantification software becomes the translator: it turns “severity” into Expected Annual Loss so leadership can act.
Mistake #2: You treat every “critical” vulnerability as equal
What’s happening
Your patch team gets flooded with “P1” items. Everything is urgent, so nothing is.
Why it fails
You create operational noise:
- SLA misses
- burn-out
- “patching theater” (activity without measurable risk reduction)
Boards don’t reward effort. They reward outcomes.
How to fix it (board-ready)
Force a hard constraint: Top 10 only.
Every week, produce:
- Top 10 vulnerabilities by risk-reduction per unit effort
- Owner + due date
- Expected risk reduction ($) if fixed
- Residual risk if deferred
This one simple operational change increases decision velocity because it turns a backlog into an investment list.
Mistake #3: Your asset inventory is incomplete (so your priorities are fiction)
What’s happening
You can’t prioritize what you can’t see:
- shadow IT
- cloud drift
- forgotten external services
- “temporary” endpoints that became permanent
Why it fails
The board hears “we patched 95% of critical vulns,” but the reality is: you patched 95% of the ones you knew about.
That’s not risk management. That’s reporting bias.
How to fix it (board-ready)
Make asset context non-negotiable:
- Business owner per asset
- Data classification per asset (regulated vs internal vs public)
- Exposure state (public, partner-accessible, internal only)
- Service dependency mapping (what breaks if it’s down)
A modern GRC platform should connect this to governance: ownership, accountability, and audit evidence: without spreadsheets.
Mistake #4: You don’t connect vulnerabilities to compliance exposure
What’s happening
Vulnerability management lives in one tool. Compliance evidence lives in another. Board reporting lives in PowerPoint. None of it is connected.
Why it fails
Regulators don’t ask, “Did you patch?” They ask:
- Do you manage risk continuously?
- Can you prove control effectiveness?
- Can you show evidence across frameworks?
If your environment touches ISO 27001, SOC 2, NIST CSF, PCI DSS, HIPAA, or GDPR, you need vulnerability work to feed the control story.
How to fix it (board-ready)
Use cybersecurity compliance software that can:
- map vulnerabilities to impacted controls (e.g., patch management, secure configuration, vulnerability remediation)
- track exceptions (risk acceptance) with business justification
- automatically attach evidence for audit cycles
This is where an integrated approach beats point tools. You stop doing compliance “after the fact.”

Mistake #5: You optimize for patch counts, not risk reduction
What’s happening
Teams celebrate:
- “We closed 1,500 tickets this month.”
Why it fails
High volume doesn’t mean high value.
A board-level program measures:
- reduction in exposure of crown-jewel assets
- reduction in Expected Annual Loss
- reduction in time-to-remediate for exploitable issues
- reduction in audit cycle time
How to fix it (board-ready)
Switch your KPI set from activity to economics:
Replace
-
of vulnerabilities closed
- % compliance with patch SLA
With
- $ risk reduced this quarter (EAL reduction)
- remediation ROI (risk reduced / cost)
- % of internet-facing critical assets with exploitable vulns
- time-to-fix for “known exploited” vulnerabilities
A strong vulnerability prioritization tool should make these metrics automatic, not a monthly manual reporting exercise.
Mistake #6: You’re blind to “right now” exploitability
What’s happening
Your prioritization model assumes all vulnerabilities are equally likely to be exploited.
Why it fails
Attackers don’t work from your backlog. They work from:
- exploit availability
- active scanning campaigns
- weak perimeter exposure
- misconfigurations combined with a single missing patch
If you prioritize without threat context, you spend time where attackers aren’t.
How to fix it (board-ready)
Blend in exploit signals:
- Known exploited status
- weaponized exploit availability
- exposure + privilege path analysis (can this lead to data access or lateral movement?)
- presence of compensating controls (is the blast radius constrained?)
This is where Observeri’s AI-driven approach matters: AI is useful when it improves the decision, not when it generates more noise. The goal is to compress your “detect → decide → remediate” loop.
Mistake #7: Your reporting doesn’t translate to the board’s language
What’s happening
Your board pack includes:
- heat maps
- CVSS averages
- “critical vulnerabilities by month”
- raw scanner charts
Why it fails
It’s not that the board doesn’t care. It’s that the board can’t fund or govern what it can’t understand.
Boards approve budgets in dollars. They govern risk in terms of business impact.
How to fix it (board-ready)
Tell a financial story, consistently, month after month:
A board-ready vulnerability narrative should include:
- Current cyber exposure in financial terms (Expected Annual Loss range)
- Top 5 drivers of loss (which assets, which weaknesses, which scenarios)
- Planned remediation investments and ROI
- Risk acceptance decisions (what you’re explicitly choosing to carry)
- Leading indicators (what will likely get worse in the next 30–90 days)
This is where cyber risk quantification software becomes the bridge between the CISO and CFO. Instead of “we need to patch more,” you get “this reduces expected loss by $X at a cost of $Y.”

A practical “Before vs After” you can steal for your next steering committee
| Area | Before (legacy VM) | After (board-ready prioritization) |
|---|---|---|
| Prioritization | CVSS sorted list | Context + exploit signals + business criticality |
| Measurement | Tickets closed | $ risk reduced + remediation ROI |
| Reporting | Technical charts | Financial narrative + decisions required |
| Compliance | Manual evidence gathering | Continuous mapping with cybersecurity compliance software |
| Operating model | Reactive patch sprints | Predictive risk reductions in 30–90 day windows |
What Observeri changes (without turning this into a “tool talk”)
Observeri is built for the operating reality enterprise teams face:
- too many findings
- too many frameworks
- too little time
- too much board pressure
By combining a GRC platform with cyber risk quantification software, plus AI-driven automation, Observeri helps you:
- Quantify exposure in financial terms (so CFOs engage)
- Prioritize vulnerabilities by what materially reduces loss (not what looks scary on CVSS)
- Map remediation work to compliance controls and evidence (so audits move faster)
- Predict which risks are likely to bite in the next 30–90 days (so you stop being surprised)
If you want to see how this looks in a real workflow, start at https://www.observeri.com/.
The executive takeaway
Vulnerability prioritization is no longer “patch the highest CVSS.” That’s an administrative loop.
A modern program does three things:
- Compress decision cycles (top actions, not top findings)
- Quantify risk in dollars (so the board can govern it)
- Predict what matters next (so you move before the breach, not after)
If you fix these 7 mistakes, you don’t just patch faster. You build a program the board can actually fund: and defend.
Want me to tailor a board-slide-ready template for reporting vulnerability prioritization in dollars (EAL), with a quarterly ROI story and a “top 10” remediation plan?

Leave a Reply